Delivering a Modern, More Transparent Government
Ensure that every dollar spent is directed toward mission-aligned priorities. Decision Lens helps agencies minimize waste and rapidly make smarter planning & funding decisions.
.webp?width=1066&height=780&name=homepage-section-compressed%20(1).webp)
Maximize the Impact of Every Dollar
It is more difficult than ever to set priorities and make tough decisions among competing demands. To overcome this challenge, organizations require an integrated, transparent, and consistent planning platform. The result is better, faster decisions… because every dollar matters.
More Efficient & Effective Government
Government recognizes the necessity of improving decision-making. Being more data driven and integrated will better align dollars to strategy. The result ensures agencies continue to improve the lives of citizens, invest in game-changing emerging technology, and guarantee America’s security and prosperity.
Put Data at the Center of Every Decision
Rely on real-time insights to make data-driven decisions at the speed of relevance.
Improve Alignment of Budgets to Strategy
Ensure every dollar across your enterprise is optimally invested in the mission.
Empower Your Workforce with Automation
Shift from cumbersome and error-prone spreadsheet-based data management
Add Agility to Execution Year
Optimize resource allocation in response to disruption of your plan’s execution.
AI-Powered Scenario Planning
Evaluate thousands of scenarios to identify the best one for your organization.
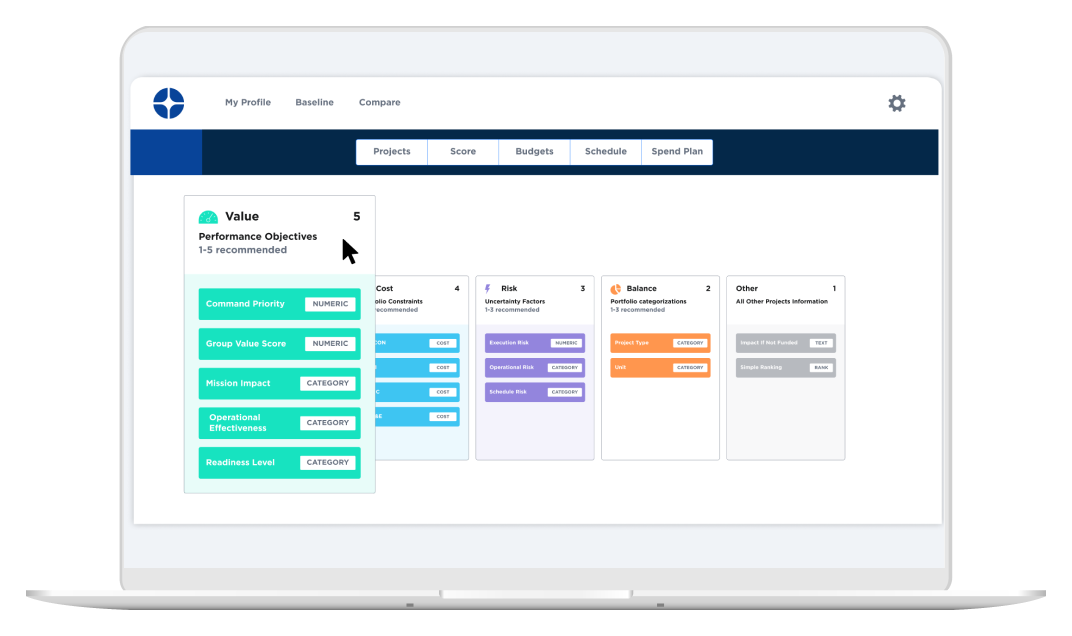
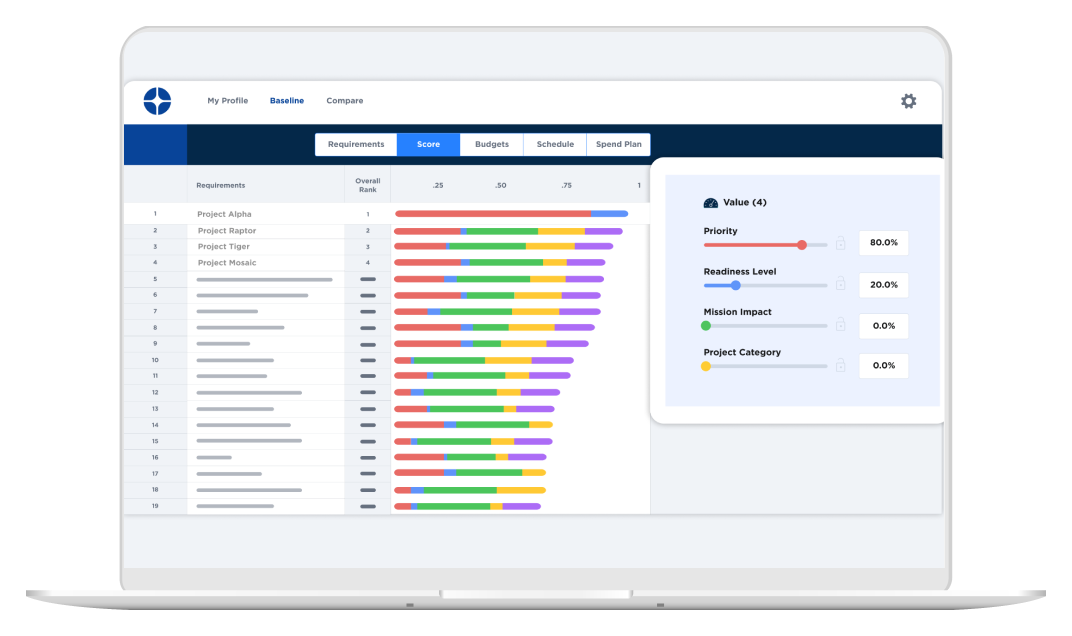
Prioritize with Purpose
Map requirements to your decision framework to create a 1-N list aligned to the strategy.
Put Your Money Where Your Mission Is
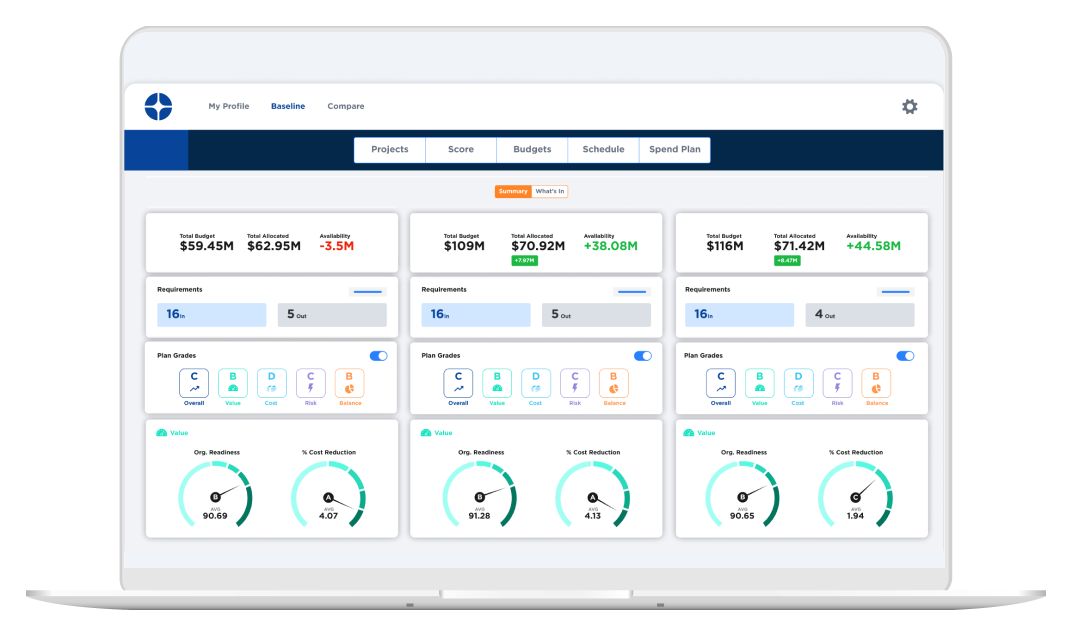
Suboptimal decisions lead to misallocated resources. With Decision Lens, organizations identify the high priority projects required to meet their objectives.
Stop Relying on Disparate, Antiquated Data
Decision Lens offers a purpose-built framework which establishes a common enterprise-wide criteria and decision language.
- Data driven decisions powered by scenario planning
- Tradeoff analysis which measures enterprise-wide impact of various courses of action
- Define and model the qualitative and quantitative data contributing to portfolio value.
From Low Value Data Validation to High Value Data Analysis
Decision Lens automates project input and maps data directly to your framework.
- Eliminate human errors by mapping inputs directly to your decision framework.
- Shift thousands of hours towards high impact strategy work and analysis
- Configureable collection form intakes input on enterprise requirements while limiting access by roles and rights.
Ready Today, Ready Tomorrow
Create an integrated operation which includes short, mid, and long-range planning time horizons.
- Amass, justify, and obtain the optimal resourcing to ensure mission success today.
- Balance future transformational investments with near-term financial constraints.
- Identify and introduce game changing capabilities to meet the future needs of citizens.
Be Ready When Conditions Change
Leverage artificial intelligence to evaluate thousands of potential scenarios to develop a justifiable strategy-aligned approach to resourcing.
- Purpose-built visuals highlight scenario impact on your goals and objectives.
- Adjust resource allocations and constraints to model and assess alternative scenarios.
- Grade the performance of each scenario against a range of potential future states.

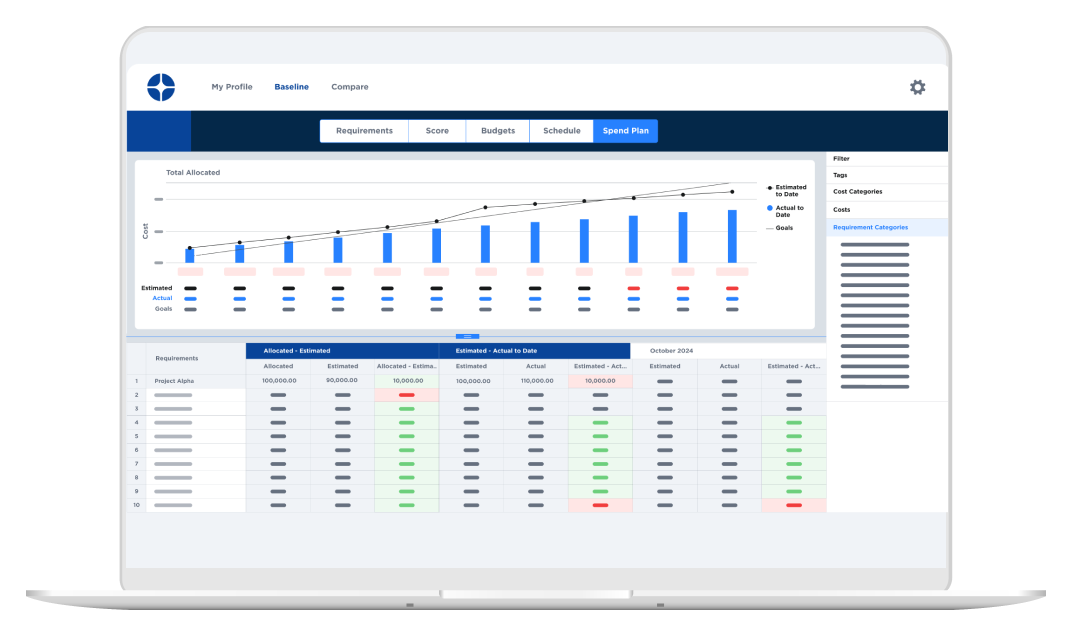
Be Prepared to Spend or Save Your Next Dollar
Monitor spending progress throughout the year to ensure funds are being utilized effectively and to avoid under- or overspending, which can impact future budget allocations.
- Real-time budget monitoring continuously tracks actual expenditures against planned budgets to identify deviations and allow you to take corrective actions
- Compare planned spend amounts against actual obligated funds to model the execution against approved budget amounts for each project.
Developed to Transform the Public Sector
Our unique software is specifically designed to modernize the public sector.
- Built-in best practices for process improvement
- Designed for rapid deployment & adoption
- Support for various IL-levels
- Available via many contracting vehicles
- Industry-leading time to value
The DoD, Federal, State and Local Agencies Rely On Our Software


























































































Top Agencies Love Decision Lens
"Decision Lens has been a game changer for how we manage and plan our supplier development funding efforts"
Deputy Director, Navy
"There is one word to describe where we are and where we are going… WOW."
Planning Director, Navy
"The software is intuitive. The flexibility and adaptability allow consistency across decision-making."
Colonel, Department of War
"Decision Lens enabled us to effectively prioritize 326 statewide projects in 3 months."
Project Planning Director, State DOT
Transforming Your Organization Starts Now
Request your custom demo and deep dive 1:1 with our experts into how we can solve the unique challenges your organization faces.